10 Appendix A – Twitter Attack 2020
In July, 2020 Twitter was hacked by a group of hackers.
The primary hacker was caught by the FBI. The FBI was able to determine location of the hacker by downloading a database of OGusers form. OGusers is a market place to buy famous social media accounts. Based on Wired Article “How the Alleged Twitter Hacker Got Caught
“The FBI located the same bitcoin wallet used by the hacker in the private message dump of OGuser form. “Investigator also used the database to connect to Chaewon’s account to another OGUsers handle, Mas. Both accounts signed onto the forums from the same IP address on the same day, according to the database leak; agents also found that multiple times between February 11 and 15 of this year, ”
OGuser “Chaewon”
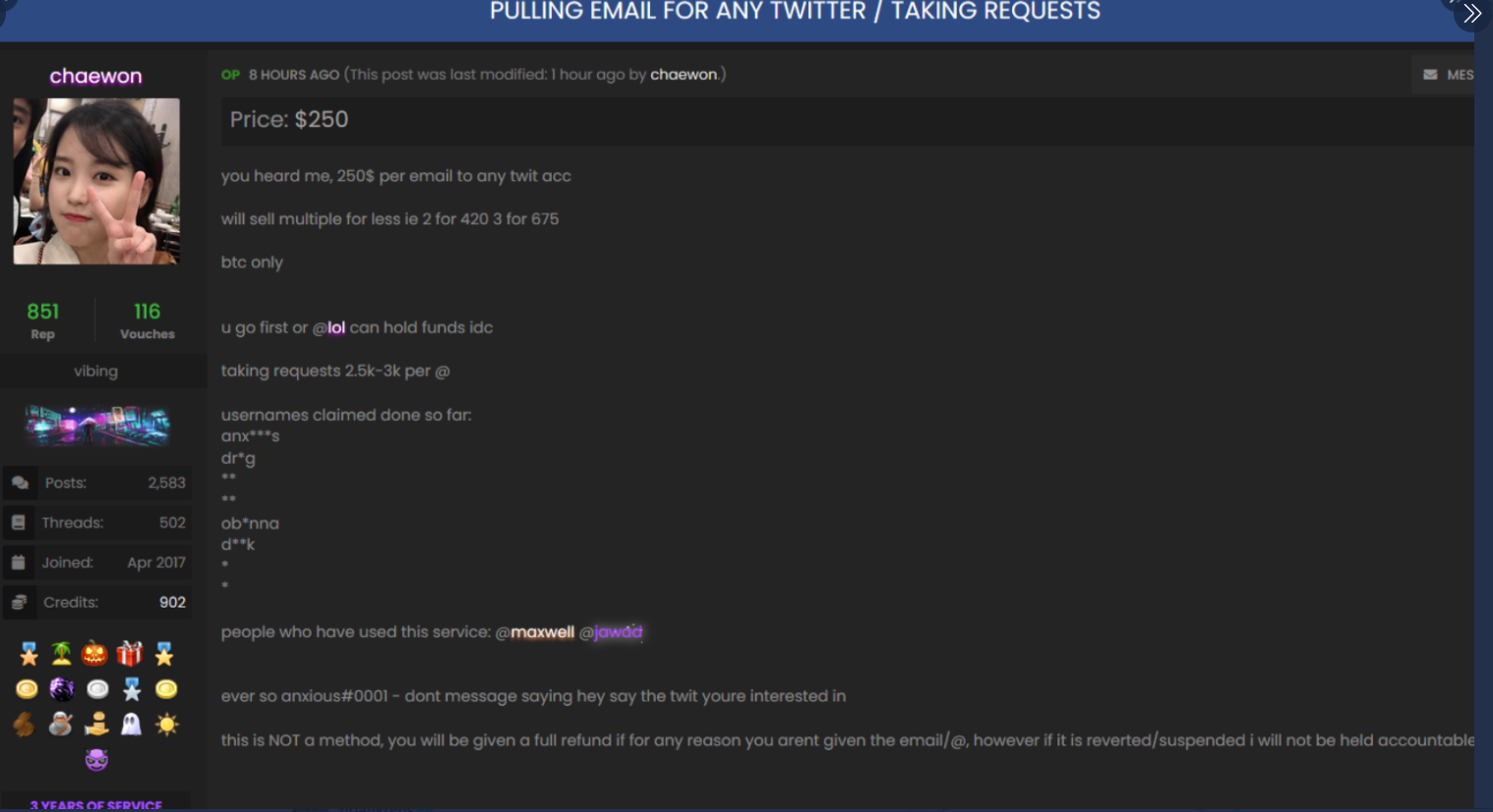
The FBI agents used IP address and bitcoin wallet to link one of the users. An OGUser used a coin base account to exchange funds, this was then tie back to the attacker. More details of the account can be read on the wired article and the court filing.
https://www.documentcloud.org/documents/7011778-Twitter-Hack-Documents.html#document/p3
How did the attacker do it?
Based on articles, OGusers used technique called sim-swapping to gain access to someone else’s phone. This requires social engineering to convince a phone company employee to provide the sim to another phone to gain access to a victims phone. Once the attacker has access to the phone, the attacker then use the phone to change password and reset accounts to the victim. In the twitter attack, the bad actor was able to obtain a phone number for a twitter employee. Once the phone number was obtain, the bad actor used social engineering to get a sim of the phone.